Guarantee Vault Platform Applicant API
Download OpenAPI specification:Download
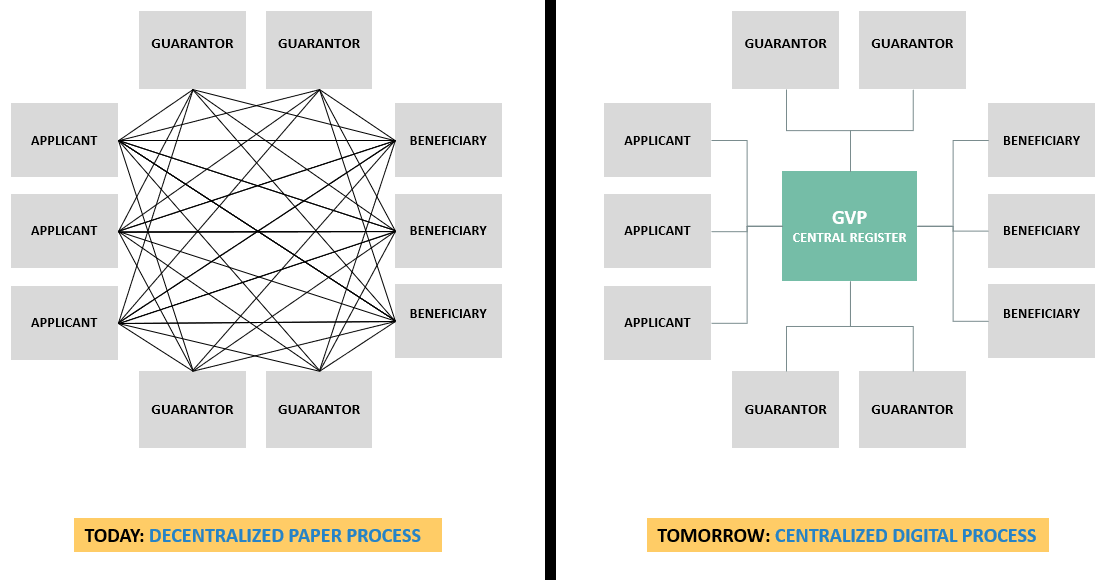
In the normal course of business, especially within the project business (e.g. construction) an applicant will need to arrange for a guarantee to be issued in favor of a beneficiary (normally its customer or buyer). The applicant will do this through a Guarantor (financial institution) that will issue the guarantee contract and be obligated by its terms. Today's challenge is that the storage of guarantees is decentralized while the guarantee related process is manual and paper based. The Guarantee Vault Platform seeks to create a centralized digital register that replaces the issued paper guarantee with its digital version. The digital guarantee would be issued by the guarantor on the GVP register and would retain the same legal authority as that held by the paper guarantee today.
GVP API looks to improve efficiency and increase transparency by replacing the decentralized paper process today with a centralized digital one that puts all market participants on the same digital page.
System Overview
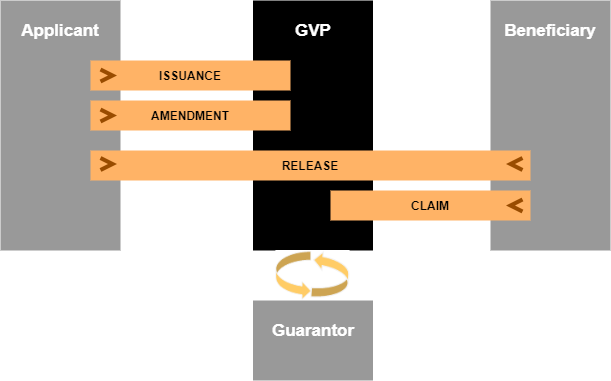
At heart, in its simplest form, the system allows:
- Applicants to request the issuance of digital guarantees
- Guarantors to accept and issue digital guarantees to beneficiaries
- Post issuance, the system allows applicants and beneficiaries to make certain requests (changes) to the issued guarantee has highlighted below.
- Issuance – Applicant only
- Amendment – Applicant only
- Release – Both Applicant & Beneficiary
- Claim – Beneficiary only
| Term/Acronym | Definition |
|---|---|
| Access Token | A credential that is used by an application to access an API. It informs the API that the bearer of the token has been authorized to access the API and perform specific actions specified by the scope that has been granted. In the case, Access Tokens are formed as JSON Web Tokens. They should be transmitted to the API as a Bearer credential in an HTTP Authorization header. |
| API | Application Programming Interface |
| Applicant | The entity whose payment or performance is secured. |
| Beneficiary | The entity to which the guarantee is issued. |
client_id | A unique ID determining the subject identified by Oauth/OpenID Connect. |
| Company | Refers to a corporate entity |
| Corporate Guarantee | Corporate Guarantee is a guarantee in which a corporation agrees to be responsible for the financial obligations of, or the performance of, contractual obligations of another party (usually its subsidiary) in the event that the other party fails to discharge his financial obligations or perform the contractual obligations. |
| DVS | Digital Vault Service GmbH company |
| Financial Institution | Refers to both banks and insurance companies |
| Guarantee | An irrevocable payment obligation of a financial institution. It serves to secure certain contractually agreed performance, warranty and/or payment obligations of the parties to the trade contracts. Payment is made on demand. The term “Guarantee” when used in this document shall refer to all of the previously defined instruments namely:
|
| Guarantor | The entity providing the guarantee, namely a financial institution e.g. Bank, Insurance Company, Corporate. |
| GVP | Guarantee Vault Platform (a product under DVS) |
| GVP Register | The electronic register where the guarantor issues a new guarantee or posts an issuance action / event. Records made available on the GVP register are legally binding as per the terms of the guarantee contract once they become accessible by other transaction party(ies). |
| JWKS URL | The URL where a Relying Party presents new JSON Web Key Sets to the GVP authorization Service without having to upload the key sets manually via the GVP Web admin GUI. |
| JWT token | JSON Web Tokens. An open, industry standard RFC 7519 method for representing claims securely between two parties. You may decode well-formed JWTs at JWT.io to view their claims. |
| Post Issuance Request | Refers to any requests coming after issuance of a guarantee from the applicant or beneficiary to the guarantor including:
|
private_key_jwt | Part of the cryptographic keypair that can be used to sign tokens that other parties can validate with the public key. |
| Refresh Token | A special kind of token that can be used to obtain a renewed Access Token. It is useful for renewing expiring Access Tokens without interrupting the integration. Using the Refresh Token, the Relying Partner can request a new Access Token at any time. Refresh Tokens can be renewed each time a new access token is requested. |
| Relying Party (RP) | The client application that supports OAuth 2.0 and relies on the OpenID provider to authenticate the end user and request claims about that user. In this case, it's the Guarantors system integrating with GVP. |
| Standby Letter of Credit (SBLC) | A lender's guarantee of payment to an interested third-party in the event the lender’s client who requested the SBLC defaults on an agreement. |
| Surety Bond (“Bürgschaft”) | A surety bond or surety (“Bürgschaft” in Germany) is a promise by a financial institution to pay one party(the obligee) a certain amount if a second party (the principal) fails to meet some obligation, such as fulfilling the terms of a contract. The surety bond protects the obligee against losses resulting from the principal's failure to meet the obligation. Surety bonds are usually validity type “Unlimited”, not payable on first demand and are a standard in Germany. Note: the surety bond (“Bürgschaft”) as such is regulated under the German Civil Code (“BGB”). |
| Unique Customer Id | The guarantors unique Customer Id for the applicant in their proprietary system. |
| Unlimited Validity | A guarantee for which the expiry is open-ended, i.e. it does not have a fixed expiry date. |
With all participants using the same platform and rules, GVP will allow for a more streamlined end to end process. Once the guarantor validates, approves and issues the guarantee, the applicant will have the possibility to make it immediately available to the beneficiary via GVP. The beneficiary at that point (whether registered with GVP or not) will then have access to the guarantee in GVP with the possibility to view details or even print the guarantee if required.
Although GVP will be available through a user interface, the majority of participants will interact with GVP using APIs to their proprietary in-house systems. This document will detail the API specifications for Applicants.
| Security Scheme Type | OAuth2 |
|---|---|
| Client OAuth Flow - RFC6749 Section 4.4 | Authorization URL: https://vault/.../oauth/token* |
Scopes
| Name | Description |
|---|---|
amendment:manage |
OpenID Connect scope for managing amendment requests |
amendment:view |
OpenID Connect scope for viewing amendment requests |
guarantee:manage |
OpenID Connect scope for managing guarantees |
guarantee-request:manage |
OpenID Connect scope for managing guarantee-requests |
guarantee-request:view |
OpenID Connect scope for viewing guarantee-requests |
guarantee:view |
OpenID Connect scope for viewing guarantees |
notification:manage |
OpenID Connect scope for managing notifications |
notification:view |
OpenID Connect scope for viewing notifications |
release:manage |
OpenID Connect scope for managing release requests |
release:view |
OpenID Connect scope for viewing release requests |
claim:manage |
OpenID Connect scope for managing claim requests |
claim:view |
OpenID Connect scope for viewing claim requests |
Authentication process
Relying Party will authenticate using its client_id (created during registration) and the private_key_jwt (according to OpenID Connect Core 1.0 chapter 9).
During the authentication process the Relying Party should generate a JWT token as described in RFC7523 section 2.2 and sign it using their private key and the RS256 algorithm (RFC7518 section 3.1).
If the Relying Party has been registered with "JWKS URL" option, the client developers should implement the corresponding endpoint on the guarantors side that returns public key(s) used for the verification. Then implementation should be done according to RFC7517 (page 10).
API Service account registration
Company admin users can create service accounts for a Relying Party. GVP system will generate a client_id for the new service account and then, the company admin will choose an application name (an informative label) and select the method to transmit the client's public key or certificate. This could be done via:
- JWKS URL endpoint (preferred)
- Manual file import
- Generating a keypair on the authorization server
The keypair will be required for the verification process. The preferred option for key handling is using the JWKS URL.
Using JWKS URL, the new keypairs will be downloaded from the client's JWKS endpoint. The other methods of communicating key-pairs will involve a manual step where company admin user re-imports the new key or certificate.
Access token expiration
Access token- expires in 1 hourRefresh token- expires in 2 hours
When the access token expires, the Relying Party shall use the refresh token in order to get a new access token or repeat the authentication process from the beginning.
Participants should implement this functionality or use any libraries that already provide a refresh token functionality “out of the box”.
Error object specification based on RFC7807
Errors that return an error object will always return a JSON object with attributes as specified below.
type- string- A URI reference [RFC3986] that identifies the problem type. This specification encourages that, when dereferenced, it provide human-readable documentation for the problem type (e.g., using HTML [W3C.REC-html5-20141028]). When this member is not present, its value is assumed to be
about:blank.
- A URI reference [RFC3986] that identifies the problem type. This specification encourages that, when dereferenced, it provide human-readable documentation for the problem type (e.g., using HTML [W3C.REC-html5-20141028]). When this member is not present, its value is assumed to be
title- string- A short, human-readable summary of the problem type. It SHOULD NOT change from occurrence to occurrence of the problem, except for purposes of localization (e.g., using) proactive content negotiation; see [RFC7231], Section 3.4).
status- number- The HTTP status code ([RFC7231], Section 6) generated by the origin server for this occurrence of the problem.
detail- string- A human-readable explanation specific to this occurrence of the problem.
instance- string- A URI reference that identifies the specific occurrence of the problem. It may or may not yield further information if dereferenced.
This API will cover the following workflow actions / scenarios
| ID | ACTION | DESCRIPTION |
|---|---|---|
| 1 | Guarantee Request | Submit a guarantee request (Applicant → GVP → Guarantor) |
| 2 | Guarantee Issuance | Receive issued guarantee (Guarantor → GVP → Applicant & Beneficiary) |
| 3 | Guarantee Return | Receive guarantee request back (Guarantor → GVP → Applicant) |
| 4 | Re-submit Guarantee Request | Send previously returned guarantee request (Applicant → GVP → Guarantor) |
| 5 | Amendment Request | Send amendment request (Applicant → GVP → Guarantor) |
| 6 | Amendment Issuance | Receive issued amendment (Guarantor → GVP → Applicant & Beneficiary) |
| 7 | Amendment Return | Receive amendment request back (Guarantor → GVP → Applicant) |
| 8 | Re-submit Amendment Request | Send previously returned amendment request (Applicant → GVP → Guarantor) |
| 9 | Re-submit Release Request | Send previously returned release request (Applicant or Beneficiary → GVP → Guarantor) |
| 10 | Release Request | Send release request (Applicant or Beneficiary → GVP → Guarantor) |
| 11 | Release Issuance | Receive issued release (Guarantor → GVP → Applicant & Beneficiary) |
| 12 | Close Issuance | Receive issued close (Guarantor → GVP → Applicant & Beneficiary) |
| 13 | Reopen Issuance | Receive issued reopen (Guarantor → GVP → Applicant & Beneficiary) |
| 14 | Claim Issuance | Receive issued claim (Guarantor → GVP → Applicant & Beneficiary) |
| 15 | Corporate Guarantee Issuance | Issue corporate guarantee (Applicant → GVP → Beneficiary) |
| 16 | Corporate Guarantee Amendment Issuance | Issue corporate guarantee amendment (Applicant → GVP → Beneficiary) |
| 17 | Corporate Guarantee Release Issuance | Issue corporate guarantee release (Applicant → GVP → Beneficiary) |
| 18 | Corporate Guarantee Claim Issuance | Issue corporate guarantee claim (Applicant → GVP → Beneficiary) |
| 19 | Corporate Guarantee Close Issuance | Issue corporate guarantee close (Applicant → GVP → Beneficiary) |
| 20 | Corporate Guarantee Reopen Issuance | Issue corporate guarantee reopen (Applicant → GVP → Beneficiary) |
| 21 | Forward Guarantee | Forward guarantee to beneficiary (Applicant → GVP → Beneficiary) |
| 22 | Ask for Guarantee Release | Send ask release request to beneficiary (Applicant → GVP → Beneficiary) |
| 23 | Certificate of Authenticity report | Retrieve certificate of authenticity report for guarantee (Applicant) |
- The API is intended for usage with a system that usually receives incoming data either in a queue or batch-based manner.
- The API assumes that the consumer of the API has a good understanding of the various steps in handling guarantees.
- The interaction of the API is based around an end-point that presents notifications.
- Notifications are references to new or changed business objects (e.g. guarantee request / issuance and post-issuance events such as amendments, releases, and claims),
- These business objects may include links related to file resources.
- The referenced business objects are expected to be downloaded and persisted in the client’s system, after which the notifications are “acknowledged”.
- The objects are available even after being acknowledged, but will never change without a notification.
- In the Guarantors system, decisions affecting the various business entities are made, and these are posted back into the GVP system as POST- or PUT-requests.
- Error/successes are being transmitted back to the client via the HTTP response.
- Successful transactions shall also appear listed in the notifications.
- PUT update requests currently need to supply a complete copy the initial POST, including attached files.
- Use ISO-8601 date format for all business-related dates in requests/responses.
Business-related dates examples: Issuance Date, Expiry Date, Reference Date, Reference Expiry Date, Release Date etc. - Use ISO-8601 datetime format for all system-generated dates in requests/responses.
System-generated dates examples: Decline date, Request Date, File Uploaded Date, Notification Creation Date etc. - All system-generated dates will be returned as datetimes in UTC
- The maximum size permitted for uploaded files is 10MB
- The maximum size allowed for requests(multipart/form-data or application/json) is 21MB
- All the date fields are allowed between years '0001' and '9999'
Unregistered Beneficiary
When submitting a guarantee request through the POST: /applicant/v0/guarantee-requests endpoint, the beneficiary can be submitted using the uuid of an already registered beneficiary. If the beneficiary is not yet registered in the GVP or the uuid is not known, the details can be provided in the guarantee request instead. The beneficairy is now known as an Unregistered Beneficiary and the GVP response includes the uuid for this beneficiary.
The GVP system will create a new entry in the Local Address Book of the consumer for any new Unregistered Beneficiary. For any subsequent request, GVP will try to identify the beneficiary now based on the beneficiary.name and beneficiary.email. If there is a matching entry already in the Local Address Book of the consumer, this beneficiary (e.g. the same uuid, address, details) will be used as a beneficiary.
Identification of incoming applications
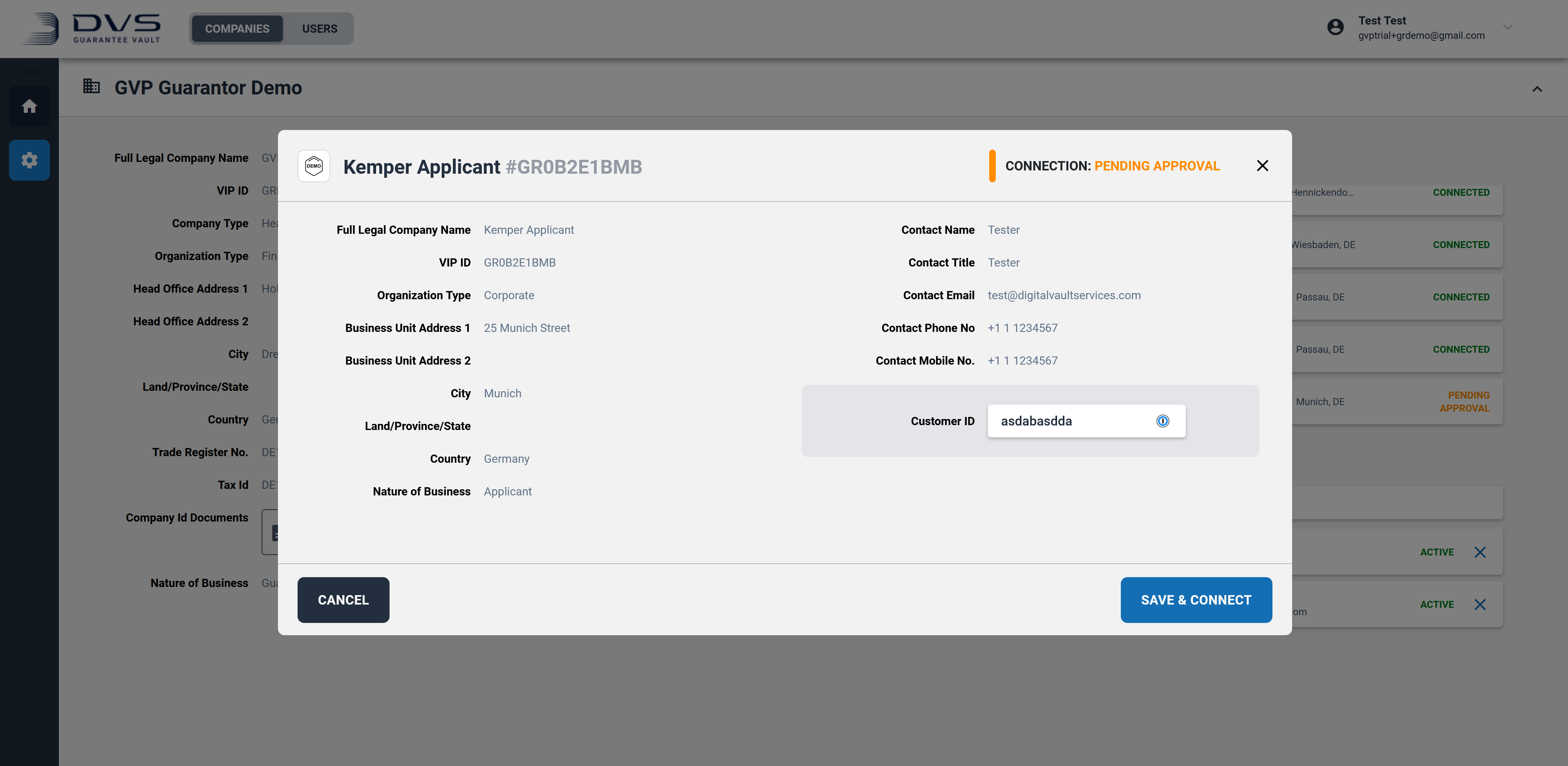
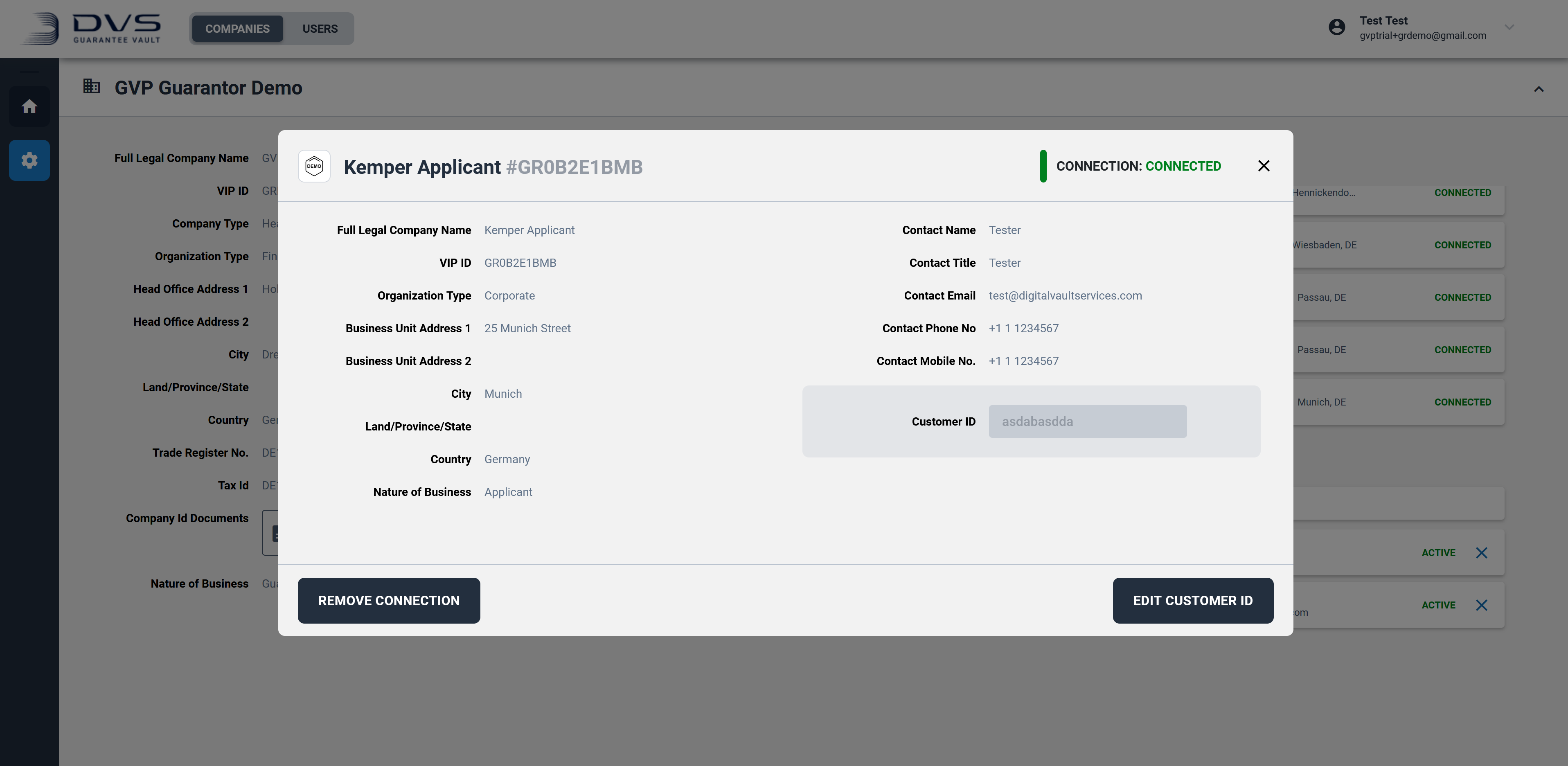
- Prior to receiving any guarantee requests from a specific applicant, the applicant admin user must submit a “connection request” to the guarantor admin via the GVP web UI.
- On accepting the “connection request” on the GVP web UI the guarantor admin will be prompted to provide their Unique Customer Id for the applicant in question
- When receiving guarantee requests from applicants via the API, GVP shall dynamically add this unique Customer Id to the incoming request allowing the guarantor to immediately identify the applicant in their proprietary system.
- The applicant sends guarantee request to GVP
- GVP dynamically adds guarantor’s unique Customer Id to the request
- As the guarantor’s system polls the notification endpoint, the guarantee request shall be listed in the notifications.
- The guarantor shall then download the guarantee request and referred attachments.
- It is expected that the data shall then be persisted in the guarantors proprietary system for financial guarantees.
- The guarantor shall then process the request at which time it shall have the following options:
- Return the request to the applicant
- In this case the guarantor shall provide a reason for the return
- The applicant shall have the possibility to edit and resubmit the request to the guarantor
- In these cases where the request has been subsequentially re-sent to the guarantor the status shall be display as
RESUBMITTED
- Issue the guarantee as requested by the applicant
- On issuance the guarantor shall provide:
- The guarantor unique reference for the guarantee
- The issuance date
- The guarantee contract
- The guarantor shall have the possibility to submit the guarantee contract as:
- Attached file (file types allowed to be confirmed)
- HTML text with format and images (to be confirmed)
- On issuance the guarantor shall provide:
- If the guarantor issues the guarantee, the records on the GVP central register are adjusted to reflect the issuance
- The applicant and beneficiary are notified and shall have access to the digital guarantee on the GVP register. The newly issued guarantee shall also appear listed in the notifications of the guarantor.
- Return the request to the applicant
As well as manually polling the notification API, any API Client can subscribe to notification events in the GVP system through Webhooks.
Configuration
Company admin user will have an option to configure the following webhook parameters for the API client:
- Payload URL - endpoint URL that will receive the webhook POST requests (will be exposed from the client side)
- Content Type - application/json or application/x-www-form-urlencoded
- Secret - the secret that will be used for HMAC signature generation(see details below)
- Activate flag - for enabling/disabling webhook
- Notification types - the notification types that the client is interested in (GUARANTEE_REQUEST, GUARANTEE, AMENDMENT, RELEASE, CLAIM, CLOSE, REOPEN)
- Version - GVP API version that API client uses (V0).
Usage
The HMAC signature will allow the API client to ensure that POST requests sent to the Payload URL are from GVP.
GVP will calculate a signature (based on a secret, the notification payload and the `HMAC SHA256` algorithm) and include it into X-Vault-Signature header in the webhook POST request as Base64-encoded hex value. The Client should implement the signature verification for these requests.
There are no retries of failed webhook deliveries and no API for listing or retrieving failed webhook events.
Therefore, the client service that exposes an endpoint for webhooks (see Payload URL) must be highly available.
In case of any issues/maintenance on client service, API client should itself request/poll /v0/notifications/new endpoint (provided by GVP) in order to get missed notifications.
The notifications received through the webhook mechanism should still be acknowledged through the Acknowledge endpoint after being persisted by the Client API.
When processing the requests to the API, different errors and exceptions can occur. The error states are listed in each request.
Most of GVP errors can be found on https://api-docs.guarantee-vault.com/errors/ErrorResponses.html
title field in response body displays exception type
type field in response body points to specific error description. For example, https://api-docs.guarantee-vault.com/errors/ErrorResponses.html#InvalidGuaranteeParticipantException
What is the purpose of the explicit Acknowledge function?
The explicit “Acknowledge” is required as the GVP system needs confirmation that each system has received the expected data.
When an Acknowledge is made by the client to GVP, GVP assumes that client received the data correctly and that it has been securely persisted into its proprietary system.
Without this explicit acknowledge, it is impossible for GVP to be certain that there were no technical difficulties and that the data was correctly received by the client’s system.
Will reporting of the items be provided via API?
Currently this is not within the scope of the API however this will be made available via the GVP web UI.
If there are any questions regarding the API of the GVP system please contact us at [email protected].
This changelog lists all additions and updates to the Guarantee Vault API, in chronological order. Changes can be in the following categories:
- [added]: Added fields, endpoints or functionality
- [changed]: Changes to existing data models
- [removed]: Removed fields or functionality
07. July 2025
- [added] New optional field
contactPersonin the guarantee data model. - [added] New additional filter parameters for
GET:guaranteesandGET:guarantee-requestsendpoints:lastChangeDateFrom,lastChangeDateTo,expiryDateFrom,expiryDateTo,guarantor.id,applicant.id,obligor.id,status. - [changed] Allow
expiryDateto be in the past for the Issue Corporate Guarantee endpoint.
14. January 2025
- [added] Endpoint 'Guarantee Reopen'
- [added] Endpoints 'Corporate Guarantee Reopen'
06. June 2024
- [added] New attachment section
guaranteeFilesLibraryadded for guarantee-request and guarantee response models - this will be filled, if wordings from the wording library feature were supplied. Supplying library wordings is currently only availiable in the GVP UI. - [changed] If
guaranteeWordingOTHER was selected, it is now also possible to provideguaranteeFilesattachments orguaranteeText.
20. November 2023
- [added] Field
governingLawSubdivisionfor specifying the Subdivision of a Governing Law Country in a Guarantee. - [changed] Field
placeOfJurisdictionin a Guarantee can only be filled ifgoverningLawis filled. - [changed] Field
deliveryAddressin a Guarantee can also be filled optionally ifAPPLICANT,BENEFICIARYorOBLIGORwas selected to capture delivery details. - [changed] Field
deliveryAddressin a Guarantee increased to 780 characters. - [changed] Field
reasonin an ask-release request increased to 1000 characters.
09. October 2023
- [changed] Limit all issuance reference fields (
issuance.ref) to 140 characters (guarantee, amendment, claim, release).
24. July 2023
- [changed] Amendment Issuance files:
minItems: 0andmaxItems: 10, not mandatory.
The notifications gives the system a list of data of various types. The client should GET the document and referenced file resources. When the client is certain that the data is persisted to its system, a call to the Acknowledgement should be made.
The various resources will be available until they are explicitly acknowledged.
New Notifications
Retrieve up to limit un-acknowledged notifications from the notification inbox. This operation can be called either with or without a notification type, if type is omitted you will receive notifications from all channels/types. The latter is the suggested default, unless integration reasons dictate otherwise.
Although the requesting client is free to acknowledge at any time soon after receiving the notification, it is preferable that the object is retrieved before doing so.
query Parameters
| type | string |
| limit | string Default: 5 |
Responses
Response samples
- 200
- 400
{- "notifications": [
- {
- "notificationId": "756ffc40-6591-4e53-88f1-9b8ba3af711a",
- "type": "GUARANTEE_REQUEST",
- "event": "GUARANTEE_REQUEST_DECLINED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-11-24T18:15:27Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": null
}, - {
- "notificationId": "989f0a3b-d24c-4f0f-9842-c241d4ec93b2",
- "type": "GUARANTEE",
- "event": "GUARANTEE_ISSUED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-11-25T09:41:26Z",
- "requestId": null,
- "guaranteeId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8"
}, - {
- "notificationId": "5a4b65c2-1e51-4c1c-a3fa-9c38b621fcb1",
- "type": "GUARANTEE",
- "event": "GUARANTEE_EXPIRED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-11-25T10:48:28Z",
- "requestId": null,
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "fe7bb94c-8d3e-44ec-8f59-b6eabe476994",
- "type": "AMENDMENT",
- "event": "AMENDMENT_REQUEST_DECLINED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-11-25T10:51:17Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "fc1059f7-fc84-4502-b17f-5ec88639fe70",
- "type": "AMENDMENT",
- "event": "AMENDMENT_REQUEST_ISSUED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-11-25T11:11:56Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "3ffe2f81-05f6-45ee-aacb-6f0a24931084",
- "type": "RELEASE",
- "event": "RELEASE_REQUEST_DECLINED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-11-25T11:13:34Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "e7696bb8-4384-4b41-a8e5-874b9359bab3",
- "type": "RELEASE",
- "event": "RELEASE_REQUEST_ISSUED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-11-25T12:52:23Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "d804c5a4-128e-473a-82d4-1972c2a23a6e",
- "type": "RELEASE",
- "event": "RELEASE_REQUEST_PUBLISHED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-10-04T14:19:22.321Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "d224c5a4-118e-488a-39d4-1972c2a23a6e",
- "type": "RELEASE",
- "event": "RELEASE_REQUEST_RESUBMITTED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-10-04T14:19:22.321Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "7248046b-97bf-461c-8901-8d1e1a0900f8",
- "type": "CLAIM",
- "event": "CLAIM_REQUEST_DECLINED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-11-25T11:13:34Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "aa242d01-c500-4b8c-93c5-6e79bc34172d",
- "type": "CLAIM",
- "event": "CLAIM_REQUEST_ISSUED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-11-25T12:52:23Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "ee9bd74e-678c-4386-8ce0-04e814645f7c",
- "type": "CLAIM",
- "event": "CLAIM_REQUEST_PUBLISHED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-10-04T14:19:22.321Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "ee9bd74e-678c-4386-8ce0-04e814645f7c",
- "type": "CLAIM",
- "event": "CLAIM_REQUEST_RESUBMITTED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-10-04T14:19:22.321Z",
- "requestId": "667e8fa3-3f80-45f9-8aab-d72eac5735a8",
- "guaranteeId": "82711181-00e3-4963-92e5-afe3a181c667"
}, - {
- "notificationId": "dba68388-6043-4278-a0aa-74e63df56386",
- "type": "CLOSE",
- "event": "CLOSE_REQUEST_ISSUED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-10-04T14:19:22.321Z",
- "requestId": "035e03ea-402b-4e2d-86a4-de4f976e157d",
- "guaranteeId": "5efbebcf-df33-41c1-8c0b-cc7951179e9c"
}, - {
- "notificationId": "41f81c6d-5167-4be0-bcab-79195a29d6e6",
- "type": "REOPEN",
- "event": "REOPEN_REQUEST_ISSUED",
- "participantRole": "APPLICANT",
- "notificationCreatedDate": "2020-10-05T14:19:22.321Z",
- "requestId": "30db68ea-51e3-4d51-8546-d91f2ad504cb",
- "guaranteeId": "5efbebcf-df33-41c1-8c0b-cc7951179e9c"
}
]
}Acknowledge Notification
Marks the notification as received, and removes it from the notification inbox.
Although the requesting client is free to acknowledge at any time soon after receiving the notification, it is preferable that the object is retrieved before doing so.
path Parameters
| notificationId required | string |
Responses
Response samples
- 200
- 400
{- "notificationId": "2d591c23-85b1-4e8c-a6bd-74d89f8955c5",
- "status": "acknowledged"
}Reject Notification
Marks the notification as rejected, saves the rejection reason and removes it from the notification inbox.
Although the requesting client is free to reject at any time soon after receiving the notification, it is preferable that the object is retrieved before doing so.
path Parameters
| notificationId required | string |
Request Body schema: application/json
| reason required | string <= 1000 characters Contains the reason for rejecting the notification |
Responses
Request samples
- Payload
{- "reason": "string"
}Response samples
- 200
- 400
{- "notificationId": "2d591c23-85b1-4e8c-a6bd-74d89f8955c5",
- "reason": "string",
- "status": "acknowledged"
}The guarantee request enables the applicant to submit a guarantee request, retrieve an overview of guarantee requests, retrieve the details of an individual guarantee request, and update a guarantee request in case it has been returned by the guarantor.
Submit a Guarantee Request
Submit a Guarantee Request to the GVP system. This makes it available for the Guarantor. If no uuid for the Beneficiary is provided, the Unregistered Beneficiary is used (see Usage of the API).
Instrument types allowed: BANK_GTEE, SURETY_BOND, STANDBY_LC, SURETY_PAYABLE_ON_FIRST_DEMAND
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
Request Body schema: multipart/form-data
required | object |
| guaranteeFiles | Array of strings <binary> [ 0 .. 10 ] items Guarantee Files If field "guaranteeWording" is set to "WORDING_APPLICANT" wording of applicant or "WORDING_BENEFICIARY" wording of beneficiary the user must either populate the field "guaranteeText" or attach file in field guaranteeFiles. If field "guaranteeWording" is set to "OTHER" the user can optionally populate guaranteeText or attach guaranteeFiles. Allowed content types:
|
| otherAttachments | Array of strings <binary> [ 0 .. 10 ] items Other Attachments Other information related to the request can be attached here. Can be multiple files Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "status": "REQUESTED",
- "guaranteeRequestId": "ca6dede1-2b1d-49f0-9c04-ba7aa9df5986",
- "instrument": "BANK_GTEE",
- "obligor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "customerRef": "00987784CHFHJ",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 4",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 4",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "guarantor": {
- "id": "bcae7774-e905-4a15-99de-d92d363d3e1d",
- "name": "Bank AG",
- "address1": "Kaiser-Joseph-Strasse 34",
- "address2": "Kaiser-Joseph-Strasse 35",
- "city": "Donauwörth",
- "country": "DE",
- "province": "Bavaria",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Bank AG",
- "line2": "Kaiser-Joseph-Strasse 34",
- "line3": "Donauwörth,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "unregistered": true,
- "language": "en",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicantRef": "Company0000345F",
- "formInstrument": "DIRECT",
- "guarantorDetailsSpecifiedBy": "APPLICANT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "specialTerms": "TERMS_EFFECTIVENESS",
- "governingLaw": "DE",
- "governingLawSubdivision": "Bavaria",
- "placeOfJurisdiction": "Munich",
- "nominalAmount": {
- "currency": "EUR",
- "value": 175000
}, - "applicableRule": "ISPR",
- "applicableRuleOther": "Under German Jurisdiction",
- "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 100000000
}, - "contractCoverage": "17.5",
- "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "deliveryType": "DIGITAL",
- "gvpDelivery": "APPLICANT_ONLY",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "comments": "Additional comment on the Guarantee",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "otherAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "issuance": {
- "id": "91c2d8ae-2d8d-4cff-9bec-a631f3cd8836",
- "ref": "GTEE9120000111-1",
- "date": "2019-08-24",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "language": "en",
- "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "correspondentGuarantor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Kern GmbH",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schwäbisch Gmünd",
- "postalCode": "92032",
- "bicCode": "AAAABBCC00",
- "shortNameAndAddress": {
- "line1": "Kern GmbH",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "approvedBy": "Approved by John Doe",
- "demandIndicator": "NMLT",
- "charges": "Charges",
- "contactPerson": "Contact Person John Doe"
}Retrieve Guarantee Requests
Retrieve Guarantee Requests up to limit for specified page. The response can be filtered
Filters
| Name | Description |
|---|---|
lastChangeDateFrom |
Date range filter, marking the beginning of the interval. Example ?lastChangeDateFrom=2025-01-01&lastChangeDateTo=2025-05-01 or ?lastChangeDateFrom=2025-01-01. Can be specified without end boundary. |
lastChangeDateTo |
Date range filter, marking the end of the interval. Example ?lastChangeDateFrom=2025-01-01&lastChangeDateTo=2025-05-01 or ?lastChangeDateTo=2025-05-01. Can be specified without begin boundary. |
expiryDateFrom |
Date range filter, marking the beginning of the interval. Example ?expiryDateFrom=2025-01-01&expiryDateTo=2025-05-01 or ?expiryDateFrom=2025-01-01. Can be specified without end boundary. |
expiryDateTo |
Date range filter, marking the end of the interval. Example ?expiryDateFrom=2025-01-01&expiryDateTo=2025-05-01 or ?expiryDateTo=2025-05-01. Can be specified without begin boundary. |
guarantor.id |
Unary filter. Example guarantor.id=46d82fd0-ee0b-4716-8b1d-a67c1ff99c97 |
applicant.id |
Unary filter. Example applicant.id=46d82fd0-ee0b-4716-8b1d-a67c1ff99c97 |
obligor.id |
Unary filter. Example obligor.id=46d82fd0-ee0b-4716-8b1d-a67c1ff99c97 |
applicantRef |
Unary filter. Example applicantRef=TGU6843 |
status |
Unary filter. Example status=ISSUED. For guarantee requests only REQUESTED, SENT, ISSUED, RESUBMITTED, RETURNED, CLOSED are supported |
query Parameters
| applicantRef | string |
| guarantor.id | string |
| applicant.id | string |
| obligorId | string |
| status | string |
| lastChangeDateFrom | string |
| lastChangeDateTo | string |
| expiryDateFrom | string |
| expiryDateTo | string |
| page | string Default: 0 |
| limit | string <= 50 Default: 5 |
Responses
Response samples
- 200
- 400
{- "guaranteeRequests": [
- {
- "status": "REQUESTED",
- "guaranteeRequestId": "ca6dede1-2b1d-49f0-9c04-ba7aa9df5986",
- "instrument": "BANK_GTEE",
- "obligor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "customerRef": "00987784CHFHJ",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 4",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 5",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "guarantor": {
- "id": "bcae7774-e905-4a15-99de-d92d363d3e1d",
- "name": "Bank AG",
- "address1": "Kaiser-Joseph-Strasse 34",
- "address2": "Kaiser-Joseph-Strasse 35",
- "city": "Donauwörth",
- "country": "DE",
- "province": "Bavaria",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Bank AG",
- "line2": "Kaiser-Joseph-Strasse 34",
- "line3": "Donauwörth,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "unregistered": true,
- "language": "en",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicantRef": "Company0000345F",
- "formInstrument": "DIRECT",
- "guarantorDetailsSpecifiedBy": "APPLICANT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "specialTerms": "TERMS_EFFECTIVENESS",
- "governingLaw": "DE",
- "governingLawSubdivision": "Bavaria",
- "placeOfJurisdiction": "Munich",
- "nominalAmount": {
- "currency": "EUR",
- "value": 175000
}, - "applicableRule": "ISPR",
- "applicableRuleOther": "Under German Jurisdiction",
- "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "lastChangeDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 100000000
}, - "contractCoverage": "17.5",
- "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "deliveryType": "DIGITAL",
- "gvpDelivery": "APPLICANT_ONLY",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "comments": "Additional comment on the Guarantee",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "guaranteeFilesLibrary": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "otherAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "issuance": {
- "id": "91c2d8ae-2d8d-4cff-9bec-a631f3cd8836",
- "ref": "GTEE9120000111-1",
- "date": "2019-08-24",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "language": "en",
- "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "declined": {
- "reason": "any return reason",
- "date": "2020-09-10T12:16:51Z"
}, - "correspondentGuarantor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Kern GmbH",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "bicCode": "AAAABBCC00",
- "shortNameAndAddress": {
- "line1": "Kern GmbH",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "approvedBy": "Approved by John Doe",
- "demandIndicator": "NMLT",
- "charges": "Charges",
- "contactPerson": "Contact Person John Doe"
}
]
}Retrieve Guarantee Request
Fetch up-to-date copy of the specified guarantee request.
path Parameters
| guaranteeRequestId required | string <uuid> |
Responses
Response samples
- 200
- 400
{- "status": "REQUESTED",
- "guaranteeRequestId": "ca6dede1-2b1d-49f0-9c04-ba7aa9df5986",
- "instrument": "BANK_GTEE",
- "obligor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "customerRef": "00987784CHFHJ",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 4",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 5",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "guarantor": {
- "id": "bcae7774-e905-4a15-99de-d92d363d3e1d",
- "name": "Bank AG",
- "address1": "Kaiser-Joseph-Strasse 34",
- "address2": "Kaiser-Joseph-Strasse 35",
- "city": "Donauwörth",
- "country": "DE",
- "province": "Bavaria",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Bank AG",
- "line2": "Kaiser-Joseph-Strasse 34",
- "line3": "Donauwörth,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "unregistered": true,
- "language": "en",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicantRef": "Company0000345F",
- "formInstrument": "DIRECT",
- "guarantorDetailsSpecifiedBy": "APPLICANT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "specialTerms": "TERMS_EFFECTIVENESS",
- "governingLaw": "DE",
- "governingLawSubdivision": "Bavaria",
- "placeOfJurisdiction": "Munich",
- "nominalAmount": {
- "currency": "EUR",
- "value": 175000
}, - "applicableRule": "ISPR",
- "applicableRuleOther": "Under German Jurisdiction",
- "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "lastChangeDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 100000000
}, - "contractCoverage": "17.5",
- "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "deliveryType": "DIGITAL",
- "gvpDelivery": "APPLICANT_ONLY",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "comments": "Additional comment on the Guarantee",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "guaranteeFilesLibrary": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "otherAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "issuance": {
- "id": "91c2d8ae-2d8d-4cff-9bec-a631f3cd8836",
- "ref": "GTEE9120000111-1",
- "date": "2019-08-24",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "language": "en",
- "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "declined": {
- "reason": "any return reason",
- "date": "2020-09-10T12:16:51Z"
}, - "correspondentGuarantor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Kern GmbH",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "bicCode": "AAAABBCC00",
- "shortNameAndAddress": {
- "line1": "Kern GmbH",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "approvedBy": "Approved by John Doe",
- "demandIndicator": "NMLT",
- "charges": "Charges",
- "contactPerson": "Contact Person John Doe"
}Update returned Guarantee Request
Update Guarantee Request in RETURNED state. All original data
will be updated. All fields not present in the body will be removed from the
original request, including the attached files.
Instrument types allowed: BANK_GTEE, SURETY_BOND, STANDBY_LC, SURETY_PAYABLE_ON_FIRST_DEMAND
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
path Parameters
| guaranteeRequestId required | string |
Request Body schema: multipart/form-data
required | object (UpdateGuaranteeRequest) |
| guaranteeFiles | Array of strings <binary> [ 0 .. 10 ] items Guarantee Files If field "guaranteeWording" is set to "WORDING_APPLICANT" wording of applicant or "WORDING_BENEFICIARY" wording of beneficiary the user must either populate the field "guaranteeText" or attach file in field guaranteeFiles.. If field "guaranteeWording" is set to "OTHER" the user can optionally populate guaranteeText or attach guaranteeFiles. Allowed content types:
|
| otherAttachments | Array of strings <binary> [ 0 .. 10 ] items Other Attachments Other information related to the request can be attached here. Can be multiple files Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "status": "REQUESTED",
- "guaranteeRequestId": "ca6dede1-2b1d-49f0-9c04-ba7aa9df5986",
- "instrument": "BANK_GTEE",
- "obligor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "customerRef": "00987784CHFHJ",
- "name": "Company business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 4",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 4",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "guarantor": {
- "id": "bcae7774-e905-4a15-99de-d92d363d3e1d",
- "name": "Bank AG",
- "address1": "Kaiser-Joseph-Strasse 34",
- "address2": "Kaiser-Joseph-Strasse 35",
- "city": "Donauwörth",
- "country": "DE",
- "province": "Bavaria",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Bank AG",
- "line2": "Kaiser-Joseph-Strasse 34",
- "line3": "Donauwörth,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "unregistered": true,
- "language": "en",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicantRef": "Company0000345F",
- "formInstrument": "DIRECT",
- "guarantorDetailsSpecifiedBy": "APPLICANT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "specialTerms": "TERMS_EFFECTIVENESS",
- "governingLaw": "DE",
- "governingLawSubdivision": "Bavaria",
- "placeOfJurisdiction": "Munich",
- "nominalAmount": {
- "currency": "EUR",
- "value": 175000
}, - "applicableRule": "ISPR",
- "applicableRuleOther": "Under German Jurisdiction",
- "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 100000000
}, - "contractCoverage": "17.5",
- "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "deliveryType": "DIGITAL",
- "gvpDelivery": "APPLICANT_ONLY",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "comments": "Additional comment on the Guarantee",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "otherAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "language": "en",
- "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "correspondentGuarantor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Kern GmbH",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "bicCode": "AAAABBCC00",
- "shortNameAndAddress": {
- "line1": "Kern GmbH",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "approvedBy": "Approved by John Doe",
- "demandIndicator": "NMLT",
- "charges": "Charges",
- "contactPerson": "Contact Person John Doe"
}The guarantee enables the applicant to retrieve the list of issued guarantees and retrieve the details of individual guarantees after issuance.
Retrieve Guarantees
Retrieve Guarantees up to limit for specified page. The response can filtered
Filters
| Name | Description |
|---|---|
lastChangeDateFrom |
Date range filter, marking the beginning of the interval. Example ?lastChangeDateFrom=2025-01-01&lastChangeDateTo=2025-05-01 or ?lastChangeDateFrom=2025-01-01. Can be specified without end boundary. |
lastChangeDateTo |
Date range filter, marking the end of the interval. Example ?lastChangeDateFrom=2025-01-01&lastChangeDateTo=2025-05-01 or ?lastChangeDateTo=2025-05-01. Can be specified without begin boundary. |
expiryDateFrom |
Date range filter, marking the beginning of the interval. Example ?expiryDateFrom=2025-01-01&expiryDateTo=2025-05-01 or ?expiryDateFrom=2025-01-01. Can be specified without end boundary. |
expiryDateTo |
Date range filter, marking the end of the interval. Example ?expiryDateFrom=2025-01-01&expiryDateTo=2025-05-01 or ?expiryDateTo=2025-05-01. Can be specified without begin boundary. |
issuanceDateFrom |
Date range filter, marking the beginning of the interval. Example ?issuanceDateFrom=2025-01-01&issuanceDateTo=2025-05-01 or ?issuanceDateFrom=2025-01-01 . Can be specified without end boundary. |
issuanceDateTo |
Date range filter, marking the end of the interval. Example ?issuanceDateFrom=2025-01-01&issuanceDateTo=2025-05-01 or ?issuanceDateTo=2025-05-01. Can be specified without begin boundary. |
guarantor.id |
Unary filter. Example guarantor.id=46d82fd0-ee0b-4716-8b1d-a67c1ff99c97 |
applicant.id |
Unary filter. Example applicant.id=46d82fd0-ee0b-4716-8b1d-a67c1ff99c97 |
obligor.id |
Unary filter. Example obligor.id=46d82fd0-ee0b-4716-8b1d-a67c1ff99c97 |
applicantRef |
Unary filter. Example applicantRef=TGU6843 |
status |
Unary filter. Example status=ISSUED. For guarantees only ISSUED & CLOSED are supported |
issuerRef |
Unary filter. Example issuerRef=BGE4775 |
query Parameters
| applicantRef | string |
| issuerRef | string |
| guarantor.id | string |
| applicant.id | string |
| obligor.id | string |
| status | string |
| lastChangeDateFrom | string |
| lastChangeDateTo | string |
| expiryDateFrom | string |
| expiryDateTo | string |
| issuanceDateFrom | string |
| issuanceDateTo | string |
| page | string Default: 0 |
| limit | string <= 50 Default: 5 |
Responses
Response samples
- 200
- 400
{- "guarantees": [
- {
- "status": "ISSUED",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "instrument": "BANK_GTEE",
- "obligor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "customerRef": "00987784CHFHJ",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company business unit 1",
- "line2": "Donnersbergerstrasse 5",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company business unit 1",
- "line2": "Donnersbergerstrasse 5",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "guarantor": {
- "id": "bcae7774-e905-4a15-99de-d92d363d3e1d",
- "name": "Bank AG",
- "address1": "Kaiser-Joseph-Strasse 34",
- "address2": "Kaiser-Joseph-Strasse 35",
- "city": "Donauwörth",
- "country": "DE",
- "province": "Bavaria",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Bank AG",
- "line2": "Kaiser-Joseph-Strasse 34",
- "line3": "Donauwörth,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "unregistered": true,
- "language": "en",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicantRef": "Company0000345F",
- "formInstrument": "DIRECT",
- "guarantorDetailsSpecifiedBy": "APPLICANT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "specialTerms": "TERMS_EFFECTIVENESS",
- "governingLaw": "DE",
- "governingLawSubdivision": "Bavaria",
- "placeOfJurisdiction": "Munich",
- "nominalAmount": {
- "currency": "EUR",
- "value": 175000
}, - "applicableRule": "ISPR",
- "applicableRuleOther": "Under German Jurisdiction",
- "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "lastChangeDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 100000000
}, - "contractCoverage": "17.5",
- "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "deliveryType": "DIGITAL",
- "gvpDelivery": "APPLICANT_ONLY",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "comments": "Additional comment on the Guarantee",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "guaranteeFilesLibrary": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "otherAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "language": "en",
- "issuance": {
- "id": "91c2d8ae-2d8d-4cff-9bec-a631f3cd8836",
- "ref": "GTEE9120000111-1",
- "date": "2019-08-24",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "additionalAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "correspondentGuarantor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Kern GmbH",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "bicCode": "AAAABBCC00",
- "shortNameAndAddress": {
- "line1": "Kern GmbH",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "demandIndicator": "NMLT",
- "charges": "Charges",
- "contactPerson": "Contact Person John Doe"
}
]
}Retrieve Guarantee
Up-to-date copy of the specified guarantee. The retrieved guarantee can be in any state.
path Parameters
| guaranteeId required | string |
Responses
Response samples
- 200
- 400
{- "status": "ISSUED",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "instrument": "BANK_GTEE",
- "obligor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "customerRef": "00987784CHFHJ",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company business unit 1",
- "line2": "Donnersbergerstrasse 5",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company business unit 1",
- "line2": "Donnersbergerstrasse 5",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "guarantor": {
- "id": "bcae7774-e905-4a15-99de-d92d363d3e1d",
- "name": "Bank AG",
- "address1": "Kaiser-Joseph-Strasse 34",
- "address2": "Kaiser-Joseph-Strasse 35",
- "city": "Donauwörth",
- "country": "DE",
- "province": "Bavaria",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Bank AG",
- "line2": "Kaiser-Joseph-Strasse 34",
- "line3": "Donauwörth,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "unregistered": true,
- "language": "en",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicantRef": "Company0000345F",
- "formInstrument": "DIRECT",
- "guarantorDetailsSpecifiedBy": "APPLICANT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "specialTerms": "TERMS_EFFECTIVENESS",
- "governingLaw": "DE",
- "governingLawSubdivision": "Bavaria",
- "placeOfJurisdiction": "Munich",
- "nominalAmount": {
- "currency": "EUR",
- "value": 175000
}, - "applicableRule": "ISPR",
- "applicableRuleOther": "Under German Jurisdiction",
- "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "lastChangeDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 100000000
}, - "contractCoverage": "17.5",
- "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "deliveryType": "DIGITAL",
- "gvpDelivery": "APPLICANT_ONLY",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "comments": "Additional comment on the Guarantee",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "guaranteeFilesLibrary": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "otherAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "language": "en",
- "issuance": {
- "id": "91c2d8ae-2d8d-4cff-9bec-a631f3cd8836",
- "ref": "GTEE9120000111-1",
- "date": "2019-08-24",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "additionalAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "correspondentGuarantor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Kern GmbH",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "bicCode": "AAAABBCC00",
- "shortNameAndAddress": {
- "line1": "Kern GmbH",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "demandIndicator": "NMLT",
- "charges": "Charges",
- "contactPerson": "Contact Person John Doe"
}Forward Guarantee
Forward the ISSUED guarantee to the Beneficiary.
The request body should be Empty.
Note: this endpoint is only applicable when the ISSUED guarantee DeliveryType is set to DIGITAL and gvpDelivery is set to APPLICANT_ONLY.
path Parameters
| guaranteeId required | string |
Responses
Response samples
- 400
{- "title": "Required field is missing",
- "status": 400,
- "detail": { },
}Ask for Guarantee Release
Submits a request to beneficiary, to release DIGITAL guarantee
path Parameters
| guaranteeId required | string |
Request Body schema: application/json
| releaseDate | string <date> Specifiy an optional release date for the guarantee. |
| reason required | string <= 1000 characters Contains the reason for the ask release request. |
Responses
Request samples
- Payload
{- "releaseDate": "2019-08-24",
- "reason": "string"
}Response samples
- 400
{- "title": "Required field is missing",
- "status": 400,
- "detail": { },
}The guarantee amendment enables the applicant to manage and process amendments to the original guarantee by submitting, retrieving and updating the amendments.
Submit an Amendment
Submit a Amendment Request to the GVP system. This makes it available for the Guarantor.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph. Operation not supported on guarantees directly issued by guarantor with form of instrument 'INDIRECT' or 'DIRECT_ADVISING'.
path Parameters
| guaranteeId required | string |
Request Body schema: multipart/form-data
required | object (SubmitAmendmentRequest) |
| guaranteeFiles | Array of strings <binary> [ 0 .. 10 ] items Guarantee Files If field "guaranteeWording" is set to "WORDING_APPLICANT" wording of applicant or "WORDING_BENEFICIARY" wording of beneficiary the user must either populate the field "guaranteeText" or attach file in field guaranteeFiles.. If field "guaranteeWording" is set to "OTHER" the user can optionally populate guaranteeText or attach guaranteeFiles. Allowed content types:
|
| attachments | Array of strings <binary> [ 0 .. 10 ] items Attachments Other information related to the request can be attached here. Can be multiple files Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "amendmentRequestId": "f62d9c3e-1bd6-4c13-9f52-d1b5092380b3",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "REQUESTED",
- "originator": "APPLICANT",
- "nominalAmount": {
- "currency": "EUR",
- "value": 3500,
- "type": "INCREASE"
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 4",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "specialTerms": "TERMS_EFFECTIVENESS",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 50000,
- "type": "NEW"
}, - "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "details": {
- "type": "OTHER",
- "info": "Sample Amendment details."
}, - "bankInformation": "some useful information from Corporate X",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "attachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "governingLaw": "DE",
- "governingLawSubdivision": "Bavaria",
- "placeOfJurisdiction": "Munich",
- "demandIndicator": "NMLT",
- "charges": "Charges",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "contactPerson": "Contact Person John Doe"
}Retrieve an Amendment
Retrieve Amendments.
path Parameters
| guaranteeId required | string |
| amendmentRequestId required | string |
Responses
Response samples
- 200
- 400
{- "amendmentRequestId": "f62d9c3e-1bd6-4c13-9f52-d1b5092380b3",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "REQUESTED",
- "originator": "APPLICANT",
- "nominalAmount": {
- "currency": "EUR",
- "value": 3500,
- "type": "INCREASE"
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 4",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "specialTerms": "TERMS_EFFECTIVENESS",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 50000,
- "type": "NEW"
}, - "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "details": {
- "type": "OTHER",
- "info": "Sample Amendment details."
}, - "bankInformation": "some useful information from Corporate X",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "guaranteeFilesLibrary": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "attachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "issuance": {
- "ref": "string",
- "date": "2019-08-24",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "declined": {
- "reason": "any return reason",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "governingLaw": "DE",
- "governingLawSubdivision": "Bavaria",
- "placeOfJurisdiction": "Munich",
- "demandIndicator": "NMLT",
- "charges": "Charges",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "guaranteeIssuance": {
- "ref": "string",
- "date": "2020-09-01",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "additionalAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "contactPerson": "Contact Person John Doe"
}Update returned Amendment
Update Amendment request in RETURNED state. All original data will be updated.
All fields not present in the body will be removed from the original Amendment request, including the attached files.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
path Parameters
| guaranteeId required | string |
| amendmentRequestId required | string |
Request Body schema: multipart/form-data
required | object (UpdateAmendmentRequest) |
| guaranteeFiles | Array of strings <binary> [ 0 .. 10 ] items Guarantee Files If field "guaranteeWording" is set to "WORDING_APPLICANT" wording of applicant or "WORDING_BENEFICIARY" wording of beneficiary the user must either populate the field "guaranteeText" or attach file in field guaranteeFiles.. If field "guaranteeWording" is set to "OTHER" the user can optionally populate guaranteeText or attach guaranteeFiles. Allowed content types:
|
| attachments | Array of strings <binary> [ 0 .. 10 ] items Attachments Other information related to the request can be attached here. Can be multiple files Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "amendmentRequestId": "f62d9c3e-1bd6-4c13-9f52-d1b5092380b3",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "REQUESTED",
- "originator": "APPLICANT",
- "nominalAmount": {
- "currency": "EUR",
- "value": 3500,
- "type": "INCREASE"
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 4",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "specialTerms": "TERMS_EFFECTIVENESS",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 50000,
- "type": "NEW"
}, - "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "details": {
- "type": "OTHER",
- "info": "Sample Amendment details."
}, - "bankInformation": "some useful information from Corporate X",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "attachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "governingLaw": "DE",
- "governingLawSubdivision": "Bavaria",
- "placeOfJurisdiction": "Munich",
- "demandIndicator": "NMLT",
- "charges": "Charges",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "contactPerson": "Contact Person John Doe"
}The guarantee release enables the applicant to retrieve the up-to-date information on the specified release.
Retrieve Guarantee Release
Up-to-date copy of the specified release. The release can be in any state.
path Parameters
| guaranteeId required | string |
| releaseRequestId required | string |
Responses
Response samples
- 200
- 400
{- "releaseRequestId": "52fa10f0-dae9-42a5-8c65-9d09b483fb63",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "REQUESTED",
- "originator": "APPLICANT",
- "requestedReleaseDate": "2019-08-24",
- "amount": {
- "currency": "EUR",
- "value": 175000
}, - "reason": "BUFI",
- "reasonOther": "We need clarification on X, Y and Z. Please refer to email sent to Klaus Smith 2020-10-13. ",
- "message": "Any useful message to Guarantor",
- "supportingDocuments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "declined": {
- "reason": "any return reason",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "contactPerson": "Contact Person John Doe",
- "issuance": {
- "ref": "string",
- "date": "2019-08-24",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}
}Update returned Release
Update Release request in RETURNED state. All original data will be updated.
All fields not present in the body will be removed from the original Release request, including the attached files.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
path Parameters
| guaranteeId required | string |
| releaseRequestId required | string |
Request Body schema: multipart/form-data
required | object (UpdateReleaseRequest) |
| supportingDocuments | Array of strings <binary> >= 0 items Supporting Documents Other information related to the request can be attached here. Can be multiple files Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "releaseRequestId": "52fa10f0-dae9-42a5-8c65-9d09b483fb63",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "REQUESTED",
- "originator": "APPLICANT",
- "amount": {
- "currency": "EUR",
- "value": 175000
}, - "reason": "BUFI",
- "reasonOther": "We need clarification on X, Y and Z. Please refer to email sent to Klaus Smith 2020-10-13. ",
- "message": "Any useful message to Guarantor",
- "supportingDocuments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "contactPerson": "Contact Person John Doe"
}Submit a Release
Submit Release Request to the GVP system. This makes it available for the Guarantor.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph. Operation not supported on guarantees directly issued by guarantor with form of instrument 'INDIRECT' or 'DIRECT_ADVISING'.
path Parameters
| guaranteeId required | string |
Request Body schema: multipart/form-data
required | object (SubmitReleaseRequest) |
| supportingDocuments | Array of strings <binary> >= 0 items Supporting Documents Other information related to the request can be attached here. Can be multiple files Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "releaseRequestId": "52fa10f0-dae9-42a5-8c65-9d09b483fb63",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "REQUESTED",
- "originator": "APPLICANT",
- "amount": {
- "currency": "EUR",
- "value": 175000
}, - "reason": "BUFI",
- "reasonOther": "We need clarification on X, Y and Z. Please refer to email sent to Klaus Smith 2020-10-13. ",
- "message": "Any useful message to Guarantor",
- "supportingDocuments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "contactPerson": "Contact Person John Doe"
}The guarantee claim enables the applicant to retrieve the up-to-date information on the specified claim request.
Retrieve a Claim
Retrieve Claim.
path Parameters
| guaranteeId required | string |
| claimRequestId required | string |
Responses
Response samples
- 200
- 400
{- "claimRequestId": "ae6cd89f-9216-4c24-8f5b-59e86a5ccecd",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "REQUESTED",
- "originator": "APPLICANT",
- "requestor": "APPLICANT",
- "amount": {
- "currency": "str",
- "value": 0
}, - "date": "2019-08-24",
- "type": "PAYM",
- "newExpiryDate": "2019-08-24",
- "text": "string",
- "accountName": "string",
- "accountNumber": "string",
- "institutionName": "string",
- "claimFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "attachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "issuance": {
- "ref": "string",
- "date": "2019-08-24",
- "action": "EXECUTE",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "declined": {
- "reason": "any return reason",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "contactPerson": "Contact Person John Doe"
}The guarantee close enables the applicant to retrieve the up-to-date information on the specified close request.
Retrieve Close Request
Up-to-date copy of the specified close request. The close request can be in ISSUED state only.
path Parameters
| guaranteeId required | string |
| closeRequestId required | string |
Responses
Response samples
- 200
- 400
{- "closeRequestId": "cb590b9d-037c-4f3f-90da-ef5d18642fed",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "ISSUED",
- "originator": "APPLICANT",
- "reason": "We need clarification on X, Y and Z. Please refer to email sent to Klaus Smith 2020-10-13. ",
- "issuance": {
- "ref": "string",
- "date": "2019-08-24",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}
}The guarantee reopen enables the applicant to retrieve the up-to-date information on the specified reopen request.
Retrieve Reopen Request
Up-to-date copy of the specified reopen request. The reopen request can be in ISSUED state only.
path Parameters
| guaranteeId required | string |
| reopenRequestId required | string |
Responses
Response samples
- 200
- 400
{- "reopenRequestId": "51f96ec6-fa36-4203-aec7-dc9d623ddc93",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "ISSUED",
- "originator": "APPLICANT",
- "reason": "We need clarification on X, Y and Z. Please refer to email sent to Klaus Smith 2020-10-13. ",
- "issuance": {
- "ref": "string",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}
}Provides the possibility for the applicant to download guarantee reports generated by GVP.
Generate the Certificate of Authenticity report
Generate the Certificate of Authenticity for an existing guarantee. The report is generated in pdf format
path Parameters
| guaranteeId required | string |
Responses
Response samples
- 400
{- "title": "Required field is missing",
- "status": 400,
- "detail": { },
}The corporate guarantee enables the user to issue corporate guarantees to beneficiaries and also expire the corporate guarantees accordingly.
Issue Corporate Guarantee
Issue Corporate Guarantee in GVP system. This makes it available for the corporate and beneficiary. If no uuid for the Beneficiary is provided, the Unregistered Beneficiary is used (see Usage of the API).
Instrument types allowed: CORPORATE_GTEE, CORPORATE_SURETY, COMFORT_LETTER, CORPORATE_SURETY_PAYABLE_ON_FIRST_DEMAND
Guarantee wordings allowed: WORDING_APPLICANT, WORDING_BENEFICIARY
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
Request Body schema: multipart/form-data
required | object (IssueCorporateGuarantee) |
| guaranteeFiles | Array of strings <binary> [ 0 .. 10 ] items Guarantee Files If field "guaranteeWording" is set to "WORDING_APPLICANT" wording of applicant or "WORDING_BENEFICIARY" wording of beneficiary the user must either populate the field "guaranteeText" or attach file in field guaranteeFiles.. If field "guaranteeWording" is set to "OTHER" the user can optionally populate guaranteeText or attach guaranteeFiles. Allowed content types:
|
| otherAttachments | Array of strings <binary> [ 0 .. 10 ] items Other Attachments Other information related to the request can be attached here. Can be multiple files Allowed content types:
|
| issuedGuaranteeFiles required | Array of strings <binary> = 1 items The Guarantee file should be supplied here. Currently only |
| additionalAttachments | Array of strings <binary> [ 0 .. 10 ] items Additional Attachments Issuer might provide extra information related to the guarantee(release letter templates, signatory book, etc) Can be multiple files. Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "status": "ISSUED",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "instrument": "BANK_GTEE",
- "obligor": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "customerRef": "00987784CHFHJ",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company business unit 1",
- "line2": "Donnersbergerstrasse 5",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company business unit 1",
- "line2": "Donnersbergerstrasse 5",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "guarantor": {
- "id": "bcae7774-e905-4a15-99de-d92d363d3e1d",
- "name": "Bank AG",
- "address1": "Kaiser-Joseph-Strasse 34",
- "address2": "Kaiser-Joseph-Strasse 35",
- "city": "Donauwörth",
- "country": "DE",
- "province": "Bavaria",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Bank AG",
- "line2": "Kaiser-Joseph-Strasse 34",
- "line3": "Donauwörth,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "unregistered": true,
- "language": "en",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "applicantRef": "Company0000345F",
- "formInstrument": "DIRECT",
- "guarantorDetailsSpecifiedBy": "APPLICANT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "governingLaw": "DE",
- "placeOfJurisdiction": "Munich",
- "nominalAmount": {
- "currency": "EUR",
- "value": 175000
}, - "applicableRule": "ISPR",
- "applicableRuleOther": "Under German Jurisdiction",
- "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 100000000
}, - "contractCoverage": "17.5",
- "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "deliveryType": "DIGITAL",
- "gvpDelivery": "APPLICANT_ONLY",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "comments": "Additional comment on the Guarantee",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "otherAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "language": "en",
- "issuance": {
- "id": "91c2d8ae-2d8d-4cff-9bec-a631f3cd8836",
- "ref": "GTEE9120000111-1",
- "date": "2019-08-24",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "additionalAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "demandIndicator": "NMLT",
- "charges": "Charges"
}The corporate guarantee amendment enables the user to manage and process amendments to the original guarantee by issuing and returning the amendments.
Issue Corporate Amendment(Applicant)
Issue Corporate Amendment in GVP system. This makes it available for the Beneficiary.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
path Parameters
| guaranteeId required | string |
Request Body schema: multipart/form-data
required | object (IssueCorporateGuaranteeAmendment) |
| guaranteeFiles | Array of strings <binary> [ 0 .. 10 ] items Guarantee Files If field "guaranteeWording" is set to "WORDING_APPLICANT" wording of applicant or "WORDING_BENEFICIARY" wording of beneficiary the user must either populate the field "guaranteeText" or attach file in field guaranteeFiles.. If field "guaranteeWording" is set to "OTHER" the user can optionally populate guaranteeText or attach guaranteeFiles. Allowed content types:
|
| attachments | Array of strings <binary> [ 0 .. 10 ] items Attachments Other information related to the request can be attached here. Can be multiple files Allowed content types:
|
| issuedGuaranteeFiles | Array of strings <binary> [ 0 .. 10 ] items The Guarantee file should be supplied here. Allowed content types:
|
| issuedGuaranteeNewFiles | Array of strings <binary> [ 0 .. 1 ] items The new Guarantee file should be supplied here. Currently only |
| issuedGuaranteeNewAdditionalAttachments | Array of strings <binary> [ 0 .. 10 ] items The Guarantee file should be supplied here. Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "amendmentRequestId": "f62d9c3e-1bd6-4c13-9f52-d1b5092380b3",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "REQUESTED",
- "originator": "APPLICANT",
- "nominalAmount": {
- "currency": "EUR",
- "value": 3500,
- "type": "INCREASE"
}, - "applicant": {
- "id": "80d0c5dd-7d0b-4b19-834d-c4e1ff70008e",
- "name": "Company SE business unit 1",
- "address1": "Donnersbergerstrasse 4",
- "address2": "Donnersbergerstrasse 5",
- "city": "Hamburg",
- "country": "DE",
- "province": "Schleswig-Holstein",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company SE business unit 1",
- "line2": "Donnersbergerstrasse 4",
- "line3": "Hamburg,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "beneficiary": {
- "id": "6dbe6c11-227f-48be-8dd1-14158aa2a4c3",
- "name": "Company GmbH industrial boilers BU1",
- "address1": "Maximilianstrasse 105",
- "address2": "Maximilianstrasse 106",
- "city": "Schwäbisch Gmünd",
- "country": "DE",
- "province": "Baden-Württemberg",
- "postalCode": "92032",
- "shortNameAndAddress": {
- "line1": "Company GmbH industrial boilers BU1",
- "line2": "Maximilianstrasse 105",
- "line3": "Schwäbisch Gmünd,92032",
- "line4": "Germany",
- "autogenerated": true
}
}, - "validity": "LIMITED",
- "expiryDate": "2020-09-23",
- "expiryCondition": "Expiry condition",
- "referenceType": "CONTRACT",
- "guaranteeType": "ADVANCE_PAY",
- "guaranteeTypeOther": "Special Warranty Guarantee",
- "guaranteeWording": "WORDING_BENEFICIARY",
- "guaranteeWordingOther": "Other guarantee wording",
- "specialTerms": "TERMS_EFFECTIVENESS",
- "referenceDate": "2020-07-23",
- "referenceExpiryDate": "2020-07-30",
- "contractNumber": "XS0000002334",
- "contractAmount": {
- "currency": "EUR",
- "value": 50000,
- "type": "NEW"
}, - "instrumentPurpose": "DELIVER & INSTALL OF CEILING PANELS X 5",
- "details": {
- "type": "OTHER",
- "info": "Sample Amendment details."
}, - "bankInformation": "some useful information from Corporate X",
- "guaranteeText": "Guarantee sample text",
- "guaranteeFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "attachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "governingLaw": "DE",
- "governingLawSubdivision": "Bavaria",
- "placeOfJurisdiction": "Munich",
- "demandIndicator": "NMLT",
- "charges": "Charges",
- "deliverTo": "APPLICANT",
- "deliveryAddress": "Company GmbH industrial boilers BU1, Maximilianstrasse 105, Schwäbisch Gmünd, Baden-Württemberg, DE",
- "deliveryMethod": "OTHR",
- "deliveryMethodDetails": "Additional Information delivery",
- "contactPerson": "Contact Person John Doe",
- "issuance": {
- "ref": "string",
- "date": "2020-09-01",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "requestor": "APPLICANT",
- "guaranteeIssuance": {
- "ref": "string",
- "date": "2020-09-01",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "additionalAttachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}
}The corporate guarantee release enables the user to release the applicant from the guarantee and return the corporate release request back to the beneficiary.
Issue Corporate Release
Release the applicant from the guarantee.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
path Parameters
| guaranteeId required | string <uuid> |
| releaseRequestId required | string <uuid> |
Request Body schema: multipart/form-data
required | object (IssueReleaseRequest) Issuance Issuance details coming from the corporate |
| issuedReleaseFiles | Array of strings <binary> >= 0 items The release issuance files should be supplied here. Currently only |
Responses
Response samples
- 200
- 400
{- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "releaseRequestId": "52fa10f0-dae9-42a5-8c65-9d09b483fb63",
- "status": "ISSUED",
- "issuance": {
- "ref": "string",
- "date": "2019-08-24",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}
}Return Corporate Release Request
Return corporate release request back to Beneficiary
path Parameters
| guaranteeId required | string <uuid> |
| releaseRequestId required | string <uuid> |
Request Body schema: application/json
| reason required | string <= 1000 characters Reason for returning the Release Request. |
Responses
Request samples
- Payload
{- "reason": "string"
}Response samples
- 200
- 400
{- "releaseRequestId": "52fa10f0-dae9-42a5-8c65-9d09b483fb63",
- "date": "2019-08-24T14:15:22Z",
- "reason": "string"
}Issue Corporate Release(Applicant)
Issue Corporate Release in GVP system. This makes it available for the Beneficiary.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
path Parameters
| guaranteeId required | string |
Request Body schema: multipart/form-data
required | object (IssueCorporateGuaranteeRelease) |
| supportingDocuments | Array of strings <binary> >= 0 items Supporting Documents Other information related to the request can be attached here. Can be multiple files Allowed content types:
|
| issuedReleaseFiles | Array of strings <binary> >= 0 items The release issuance files should be supplied here. Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "releaseRequestId": "52fa10f0-dae9-42a5-8c65-9d09b483fb63",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "REQUESTED",
- "originator": "APPLICANT",
- "amount": {
- "currency": "EUR",
- "value": 175000
}, - "reason": "BUFI",
- "reasonOther": "We need clarification on X, Y and Z. Please refer to email sent to Klaus Smith 2020-10-13. ",
- "message": "Any useful message to Guarantor",
- "supportingDocuments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe",
- "contactPerson": "Contact Person John Doe",
- "issuance": {
- "ref": "string",
- "date": "2020-09-01",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}, - "requestor": "APPLICANT",
- "requestedReleaseDate": "2019-08-24"
}The corporate guarantee claim enables the user to demand for an amount of money be sent to beneficiary based on the value of the guarantee. The claim will reduce the nominal amount of the guarantee.
Issue Corporate Claim(Applicant)
Issue Corporate Claim in GVP system. This makes it available for the Beneficiary.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
path Parameters
| guaranteeId required | string |
Request Body schema: multipart/form-data
required | object (IssueCorporateGuaranteeClaim) |
| claimFiles | Array of strings <binary> [ 0 .. 10 ] items Claim Files The client must either populate the Text of Claim field or attach file in field "claimFiles" Allowed content types:
|
| attachments | Array of strings <binary> [ 0 .. 10 ] items Attachments Other information related to the request can be attached here. Can be multiple files Allowed content types:
|
| claimAttachments | Array of strings <binary> >= 0 items References to Guarantee Claim Issuance files from issuing party. Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "claimRequestId": "ae6cd89f-9216-4c24-8f5b-59e86a5ccecd",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "REQUESTED",
- "originator": "APPLICANT",
- "requestor": "APPLICANT",
- "amount": {
- "currency": "str",
- "value": 0
}, - "date": "2019-08-24",
- "type": "PAYM",
- "newExpiryDate": "2019-08-24",
- "text": "string",
- "accountName": "string",
- "accountNumber": "string",
- "institutionName": "string",
- "claimFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "attachments": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "issuance": {
- "ref": "string",
- "date": "2020-09-01",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
], - "action": "EXECUTE"
}, - "sent": {
- "name": "Company SE business unit 1",
- "date": "2020-09-10T12:16:51Z"
}, - "declined": {
- "reason": "any return reason",
- "date": "2020-09-10T12:16:51Z"
}, - "approvedBy": "Approved by John Doe"
}Issue Corporate Claim Request(Beneficiary)
Claims are issued after processing claim requests sent in by the Beneficiary. The Claim Request contains details which should render an updated Guarantee Document, which is sent in on the issuance of the claim.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
path Parameters
| guaranteeId required | string |
| claimRequestId required | string |
Request Body schema: multipart/form-data
required | object (IssueIncomingCorporateClaimRequest) |
| claimAttachments | Array of strings <binary> >= 0 items References to Guarantee Claim Issuance files from issuing party. Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "claimRequestId": "ae6cd89f-9216-4c24-8f5b-59e86a5ccecd",
- "status": "ISSUED",
- "issuance": {
- "ref": "string",
- "date": "2019-08-24",
- "action": "EXECUTE",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}
}Return Corporate Claim Request
Return corporate guarantee claim request back to Beneficiary
path Parameters
| guaranteeId required | string <uuid> |
| claimRequestId required | string <uuid> |
Request Body schema: application/json
| reason required | string <= 1000 characters Reason for returning the Claim. |
Responses
Request samples
- Payload
{- "reason": "string"
}Response samples
- 200
- 400
{- "claimRequestId": "ae6cd89f-9216-4c24-8f5b-59e86a5ccecd",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "date": "2019-08-24T14:15:22Z",
- "reason": "string"
}The corporate guarantee close enables the user to expire the guarantee. An issued request will close the guarantee.
Issue Corporate Close
Issue Corporate Close in GVP system. This makes it available for the Beneficiary.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
path Parameters
| guaranteeId required | string |
Request Body schema: multipart/form-data
required | object (IssueClose) |
| issuedCloseFiles | Array of strings <binary> >= 0 items The close issuance files should be supplied here. Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "closeRequestId": "cb590b9d-037c-4f3f-90da-ef5d18642fed",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "ISSUED",
- "originator": "APPLICANT",
- "reason": "We need clarification on X, Y and Z. Please refer to email sent to Klaus Smith 2020-10-13. ",
- "issuance": {
- "ref": "string",
- "date": "2020-09-01",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}
}The corporate guarantee reopen enables the user to reopen the guarantee. An issued request will set the guarantee into issued state.
Issue Corporate Reopen
Issue Corporate Reopen in GVP system. This makes it available for the Beneficiary.
For detailed information about the maximum size permitted for uploaded file and for the request overall, please read API usage paragraph.
path Parameters
| guaranteeId required | string |
Request Body schema: multipart/form-data
required | object (IssueReopen) |
| issuedReopenFiles | Array of strings <binary> >= 0 items The reopen issuance files should be supplied here. Allowed content types:
|
Responses
Response samples
- 200
- 400
{- "reopenRequestId": "51f96ec6-fa36-4203-aec7-dc9d623ddc93",
- "guaranteeId": "ed62b7ef-5f7e-440e-ac76-46a77832e008",
- "status": "ISSUED",
- "originator": "APPLICANT",
- "reason": "We need clarification on X, Y and Z. Please refer to email sent to Klaus Smith 2020-10-13. ",
- "issuance": {
- "ref": "string",
- "issuanceFiles": [
- {
- "id": "c3ff6da2-97f1-42e7-bd0d-c28881b3609e",
- "blobName": "00e1d43e-2c23-4e70-899b-3397dbe1941example-file.pdf",
- "name": "example-file.pdf",
- "date": "2021-08-25T09:11:43.712Z",
}
]
}
}